In this blog, we will learn how to install, update, remove, find packages, manage packages and repositories on Linux systems…
Spawning Interactive Reverse Shell
Shell Spawning Python pty Module python -c ‘import pty; pty.spawn(“/bin/sh”)’ Perl perl -e ‘exec “/bin/sh”;’ Simple Shells to Fully…
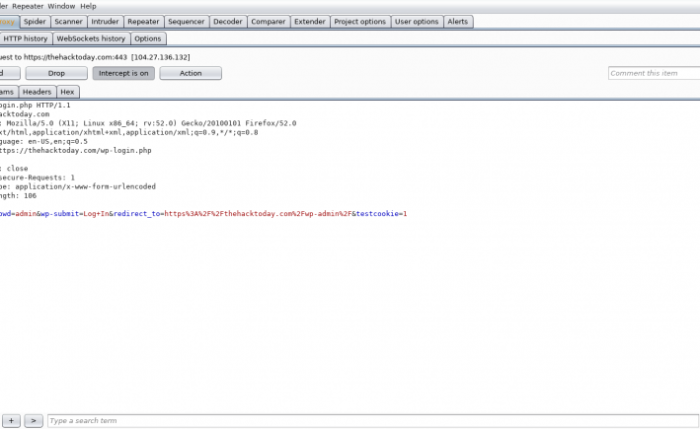
Attacking & Exploitation Researchers discovered an ongoing malvertising (online advertising to spread malware.)campaign targeting millions of WordPress websites to infect…
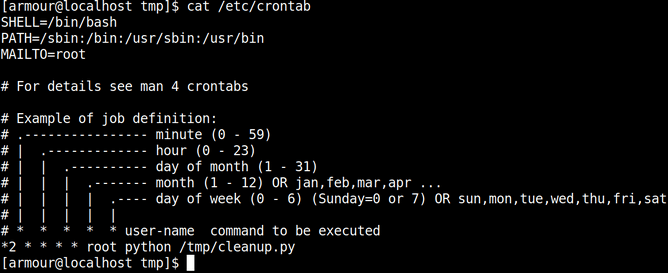
Linux Privilege Escalation by Exploiting Cronjobs
In this blog I will share procedure to enumerate and exploit Cronjob. Before going for exploitation of cronjob we are…
WordPress Enumeration
Introduction to WordPress Security WordPress is the application behind more than 35% of all websites. Its ease of use and…
Hacking with Netcat : A Comprehensive Guide
Netcat is a featured networking utility tool which reads and writes data across network connections, using the TCP/IP protocol. It…
How does the Nmap become a leading tool to scan a Network
How does the Nmap become a leading tool to Scan a Network:-
A story behind the Nmap started in 1997 with the initial announcement of Nmap by its Author named Gordon Lyon and could be found by the name of Fyodor. The aim is to Scan the Network without paying a single coin. The Initial release of…